New Code-injecting SOREBRECT Fileless Ransomware detected
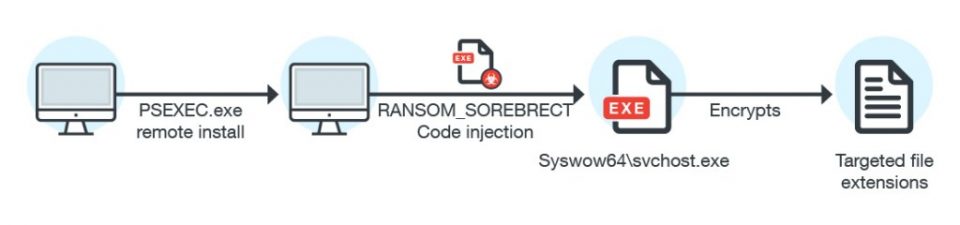
Security researchers have recently discovered a new fileless ransomware, dubbed “Sorebrect,” which injects malicious code into a legitimate system process (svchost.exe) on a targeted system and then self-destruct itself in order to evade detection.
While new forms of cybercrime are on the rise, traditional activities seem to be shifting towards more clandestine techniques that come with limitless attack vectors with low detection rates.
It is no secret that hackers and cybercriminals are becoming dramatically more adept, innovative, and stealthy with each passing day.
Unlike traditional ransomware, Sorebrect has been designed to target enterprise’s servers and endpoint. The injected code then initiates the file encryption process on the local machine and connected network shares.
This fileless ransomware first compromises administrator credentials by brute forcing or some other means and then uses Microsoft’s Sysinternals PsExec command-line utility to encrypt files.
“PsExec can enable attackers to run remotely executed commands, instead of providing and using an entire interactive login session, or manually transferring the malware into a remote machine, like in RDPs,” .
Sorebrect Also Encrypts Network Shares
Sorebrect also scans the local network for other connected computers with open shares and locks files available on them as well.
“If the share has been set up such that anyone connected to it has read-and-write access to it, the share will also be encrypted,” researchers say.
The nasty ransomware then deletes all event logs (using wevtutil.exe) and shadow copies (using vssadmin) on the infected machine that could provide forensic evidence such as files executed on the system and their timestamps, which makes this threat hard-to-detect.
In addition, Sorebrect uses the Tor network protocol in an attempt to anonymize its communication with its command-and-control (C&C) server, just like almost every other malware.
Sorebrect Ransomware Spreads Worldwide
The Sorebrect fileless ransomware has been designed to target systems from various industries including manufacturing, technology, and telecommunications.
According to Trend Micro, Sorebrect was initially targeting Middle Eastern countries like Kuwait and Lebanon, but from last month, this threat has started infecting people in Canada, China, Croatia, Italy, Japan, Mexico, Russia, Taiwan, and the U.S.
“Given ransomware’s potential impact and profitability, it wouldn’t be a surprise if SOREBRECT turns up in other parts of the world, or even in the cybercriminal underground where it can be peddled as a service,” the researchers note.
SOREBRECT’s code injection makes it a fileless threat
SOREBRECT’s attack chain involves the abuse of PsExec, a legitimate, Windows command-line utility that lets system administrators execute commands or run executable files on remote systems. The misuse of PsExec to install SOREBRECT indicates that administrator credentials have already been compromised, or remote machines were exposed or brute-forced. SOREBRECT isn’t the first family to misuse PsExec—SAMSAM, Petya, and its derivative, PetrWrap (RANSOM_SAMSAM and RANSOM_PETYA, respectively), for instance, use PsExec to install the ransomware on compromised servers or endpoints.
SOREBRECT takes this a notch further by maliciously deploying PsExec and performing code injection. It injects its code into Windows’ svchost.exe process, while the main binary self-destructs. The combination is potent: once the deployed ransomware binary finishes execution and self-termination, the injected svchost.exe—a legitimate Windows service-hosting system process—resumes the execution of the payload (file encryption). Because SOREBRECT becomes fileless after code injection, sourcing its binary sample at the endpoint level is challenging.
Why PsExec? While attackers can both use Remote Desktop Protocol (RDP) and PsExec to install SOREBRECT in the affected machine, its code injection capability makes the attack more effective. Compared to using RDP, utilizing PsExec is simpler and can take advantage of SOREBRECT’s fileless and code injection capabilities. PsExec can enable attackers to run remotely executed commands, instead of providing and using an entire interactive log-in session, or manually transferring the malware into a remote machine, like in RDPs. In SOREBRECT’s case, it makes more sense for the attackers to use PsExec since once the main binary is executed, the svchost.exe process injected with malicious code can still carry out the payload.
To cover its tracks, SOREBRECT also utilizes wevtutil.exe to delete the system’s event logs, and vssadmin to delete shadow copies. The svhost.exe process that was injected with malicious code executes the payload—encrypting the files of the local machine and network shares. SOREBRECT uses the Tor network protocol to anonymize its connection to its command-and-control (C&C) server.
SOREBRECT appends encrypted files with a .pr0tect extension

One of SOREBRECT’s ransom notes
Ways to Protect Against Ransomware Attacks
Since the ransomware does not target individuals but organizations, sysadmins and information security professionals can protect themselves by:
- Restricting user write permissions: a significant factor that exposes network shares to ransomware by giving users full permissions. By using Active Directory Group Policy Software Restriction settings this can be achieved.
- Limiting privilege for PsExec: Limit PsExec and provide permission to run them only to system administrators. Blocking TCP ports 135 & 445 for external network and Disabling Admin$ and IPC$ shares might just do the trick.
- Keeping your system and network up-to-date: Always keep your operating system, software, and other applications updated. Microsoft’s System Center Configuration Manager [SCCM] might be a very handy Solutions for this.
- Backing up your data regularly: To always have a tight grip on all your important files and documents, keep a good backup routine in place that makes their copies to an external storage device that is not always connected to your PC. AS per my personal choice Synology NAS Solution can give you a nice boost and it is cheap also.
- Adopting a cyber security-aware workforce: Educating your employees about malware, threat vectors and security measure always plays a major role in any organization.